Cybersecurity researchers have turned the spotlight on a new wave of offensive cyberattacks targeting Palestinian activists and entities starting around October 2021 using politically-themed phishing emails and decoy documents.
The intrusions are part of what Cisco Talos calls a longstanding espionage and information theft campaign undertaken by the Arid Viper hacking group using a Delphi-based implant called Micropsia dating all the way back to June 2017.
The threat actor's activities, also tracked under the monikers Desert Falcon and the APT-C-23, were first documented in February 2015 by Kasperksy and subsequently in 2017, when Qihoo 360 disclosed details of cross-platform backdoors developed by the group to strike Palestinian institutions.
The Russian cybersecurity company-branded Arid Viper the "first exclusively Arabic APT group."
Then in April 2021, Meta (formerly Facebook), which pointed out the group's affiliations to the cyber arm of Hamas, said it took steps to boot the adversary off its platform for distributing mobile malware against individuals associated with pro-Fatah groups, the Palestinian government organizations, military and security personnel, and student groups within Palestine.
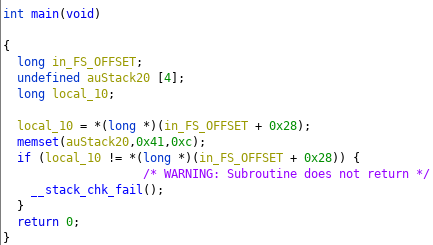
Decoy document containing text on Palestinian reunification
The raft of new activity relies on the same tactics and document lures used by the group in 2017 and 2019, suggesting a "certain level of success" despite a lack of change in their tooling. More recent decoy files reference themes of Palestinian reunification and sustainable development in the territory that, when opened, lead to the installation of Micropsia on compromised machines.
The backdoor is designed to give the operators an unusual range of control over the infected devices, including the ability to harvest sensitive information and execute commands transmitted from a remote server, such as capturing screenshots, recording the current activity log, and downloading additional payloads.
"Arid Viper is a prime example of groups that aren't very advanced technologically, however, with specific motivations, are becoming more dangerous as they evolve over time and test their tools and procedures on their targets," researchers Asheer Malhotra and Vitor Ventura said.
"These [remote access trojans] can be used to establish long-term access into victim environments and additionally deploy more malware purposed for espionage and stealing information and credentials."
Related word